Restaking Slashing
Restaking Slashing: Enhanced Penalty Risks
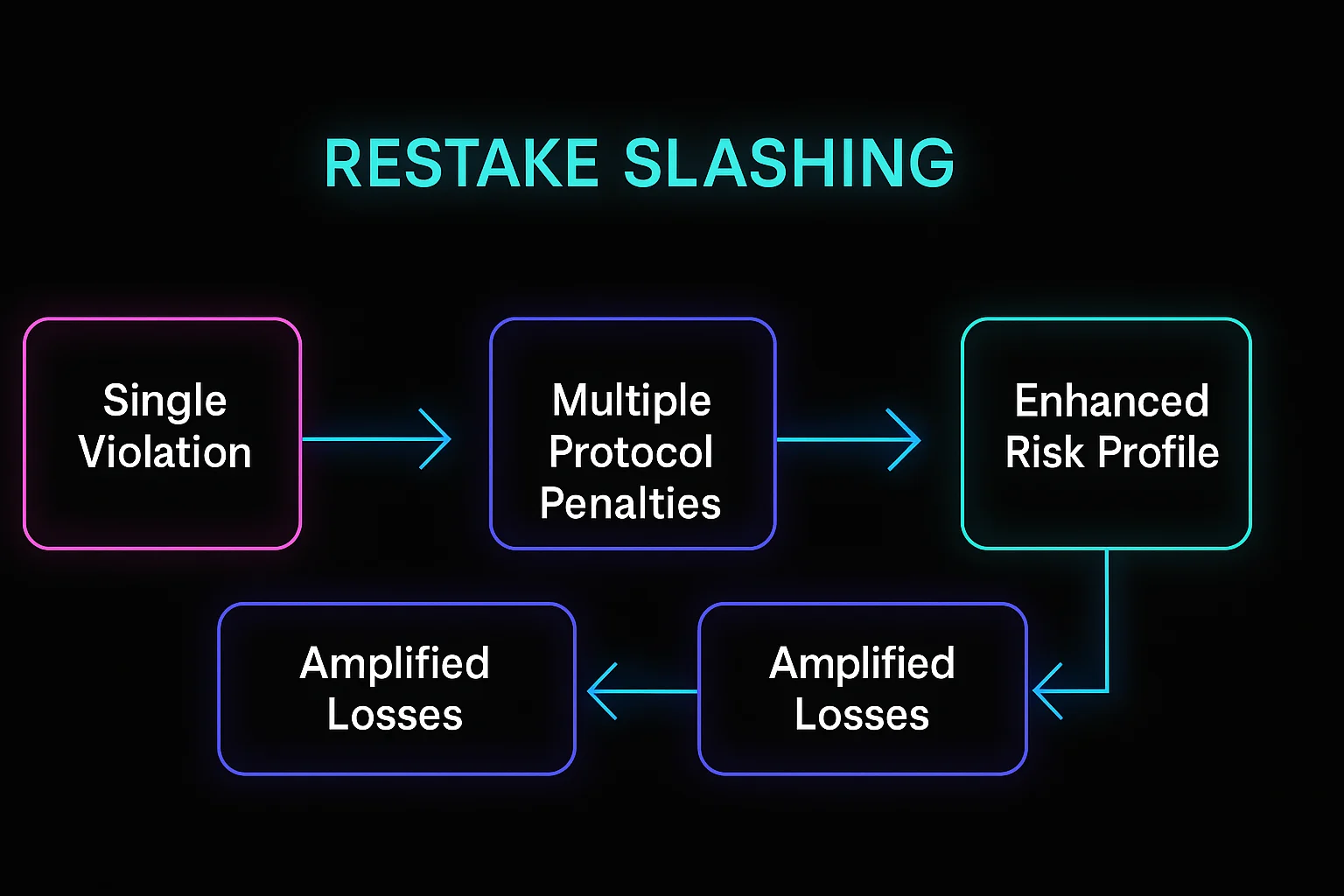
Restaking slashing involves penalties from multiple protocols simultaneously, amplifying potential losses for validators who secure additional networks. It’s like being liable for multiple insurance policies with a single accident.
Restaking slashing refers to the enhanced penalty mechanisms that apply when validators use restaked assets to secure multiple protocols, potentially facing slashing from multiple sources for single violations. This creates compounded risk but also enhanced rewards.
How Restaking Slashing Works
Multiple slashing conditions from different protocols can trigger simultaneously, creating larger penalty exposure than traditional single-protocol staking.
Cascading failures may occur when slashing in one protocol affects the validator’s ability to meet requirements in other protocols they’re securing.
Risk amplification means validators face greater potential losses in exchange for earning rewards from multiple sources simultaneously.
Real-World Examples
- EigenLayer restaking creates exposure to slashing from both Ethereum and additional protocol violations
- Babylon Bitcoin staking introduces slashing mechanisms to normally non-slashable Bitcoin
- Various middleware protocols that add their own slashing conditions to base layer stakes
Why Beginners Should Care
Risk multiplication requires careful consideration of whether enhanced yields justify significantly increased slashing exposure.
Operator selection becomes more critical when choosing validators who must competently manage multiple protocol requirements.
Insurance considerations may become important for large restaking positions given the amplified penalty risks.
Related Terms: Restaking, Slashing, Validator, Risk Management
