zkSync
zkSync: Ethereum’s Zero-Knowledge Scaling
zkSync is a Layer 2 scaling solution that uses zero-knowledge proofs to bundle transactions while maintaining Ethereum’s security. It’s like having an express lane that’s mathematically guaranteed to follow traffic laws.
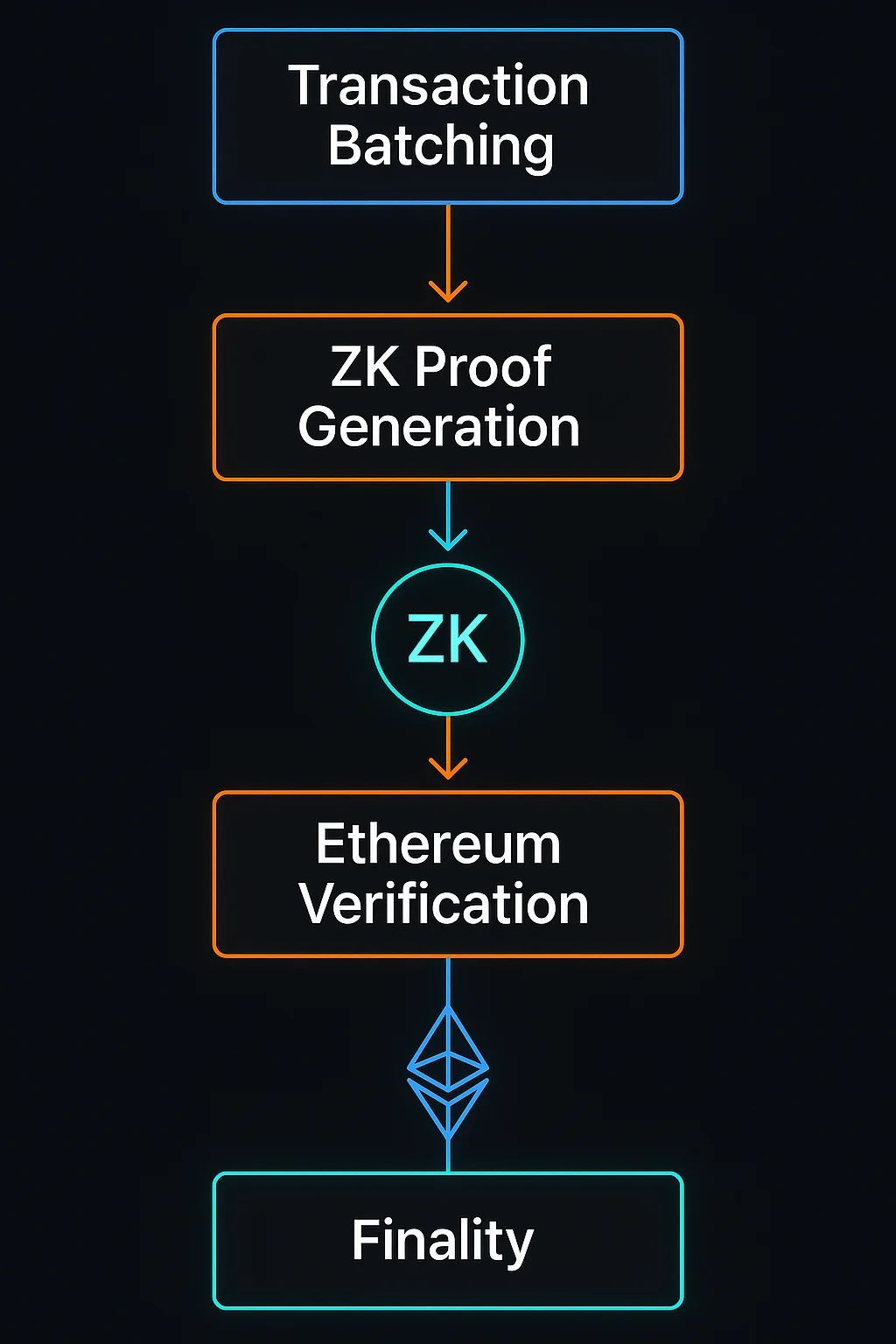
zkSync is a zero-knowledge rollup that scales Ethereum by processing transactions off-chain and submitting cryptographic proofs of validity to the main network. It enables faster, cheaper transactions while inheriting Ethereum’s security guarantees.
How zkSync Works
Zero-knowledge proofs validate transaction bundles without revealing individual transaction details, enabling privacy and scalability simultaneously.
Batch processing combines hundreds of transactions into single proofs that get submitted to Ethereum, dramatically reducing per-transaction costs.
EVM compatibility (in zkSync Era) allows existing Ethereum applications to deploy without modification while benefiting from improved performance.
Real-World Examples
- zkSync Era supports full EVM compatibility for seamless dApp migration from Ethereum
- Major DeFi protocols have deployed on zkSync for lower fees and faster confirmation
- NFT marketplaces use zkSync to reduce minting and trading costs significantly
Why Beginners Should Care
Significant cost savings compared to Ethereum mainnet while maintaining the same security guarantees through mathematical proofs.
Faster finality for most transactions since ZK proofs provide immediate validity confirmation rather than requiring fraud proof waiting periods.
Technical complexity in ZK proof generation creates different trade-offs compared to optimistic rollups, affecting developer experience and computational requirements.
Related Terms: Zero-Knowledge Proof, Layer 2, Rollups, EVM Compatibility
