Multisig Recovery
Multisig Recovery: Getting Back Lost Access
Multisig recovery helps regain access to multi-signature wallets when some keys are lost or compromised. It’s like having spare keys for your house, but with cryptographic mathematics.
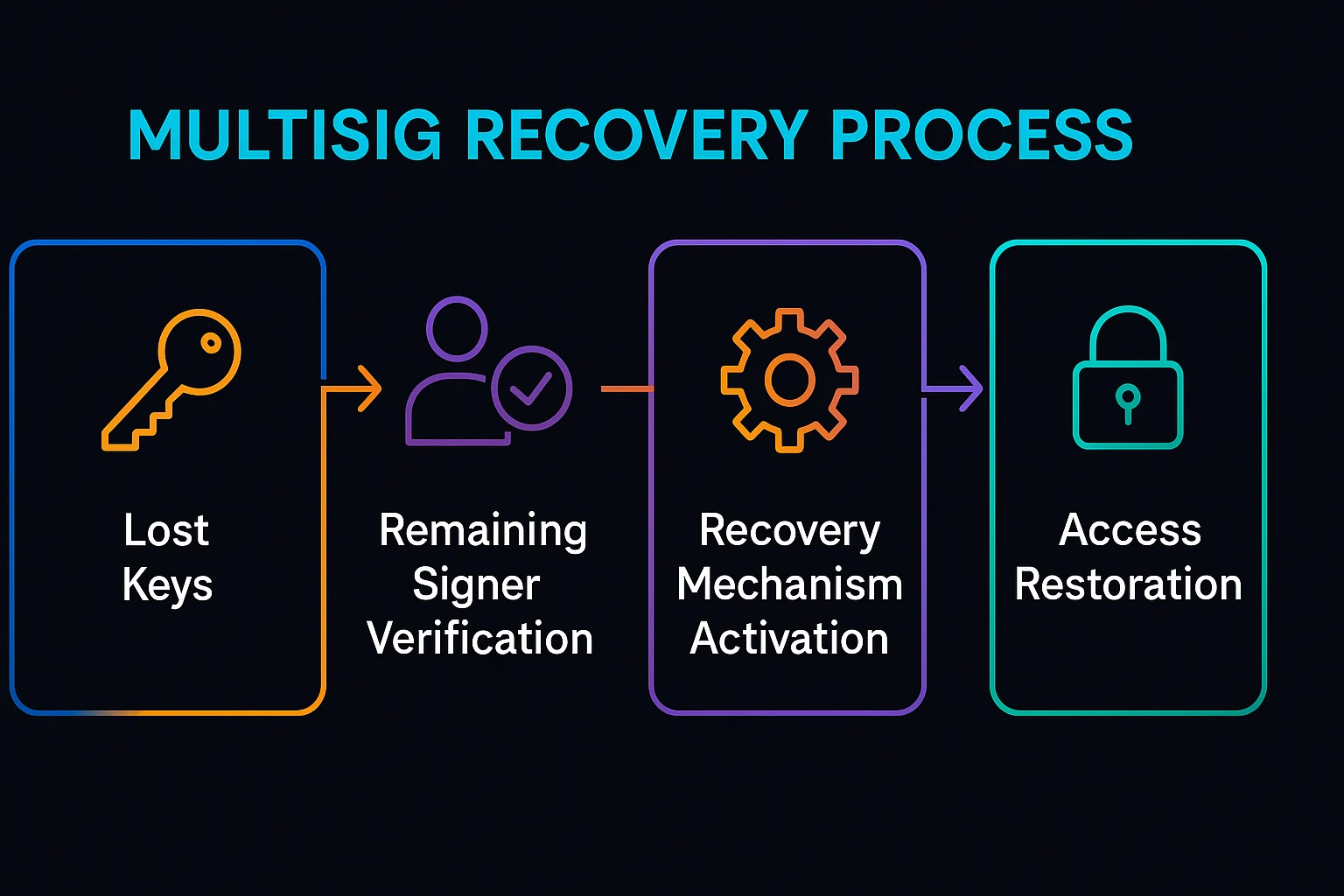
Multisig recovery refers to mechanisms that restore access to multi-signature wallets when the required number of signatures is no longer available due to lost keys, compromised devices, or unavailable signers. Recovery methods must balance security with accessibility.
How Multisig Recovery Works
Threshold adjustment may allow reducing signature requirements during recovery procedures, typically requiring unanimous consent from remaining key holders.
Timelock recovery enables predetermined recovery procedures that activate after extended periods of inactivity, allowing backup methods to restore access.
Social recovery involves trusted contacts who can collectively restore access through predetermined procedures when primary key holders are unavailable.
Real-World Examples
- Gnosis Safe recovery modules enable timelock-based recovery procedures for multi-signature wallets
- Argent wallets use social recovery with trusted guardians to restore access
- Corporate treasury recovery procedures for when key employees leave or become unavailable
Why Beginners Should Care
Access preservation prevents permanent loss of funds when multisig signers become unavailable due to device loss, death, or other circumstances.
Security trade-offs as recovery mechanisms can potentially be exploited if not designed carefully, creating new attack vectors.
Planning importance requires establishing recovery procedures before they’re needed, when all parties are available to configure them properly.
Related Terms: Multi-Signature, Social Recovery, Timelock, Wallet Security
