AML (Anti-Money Laundering)
AML (Anti-Money Laundering): Fighting Financial Crime
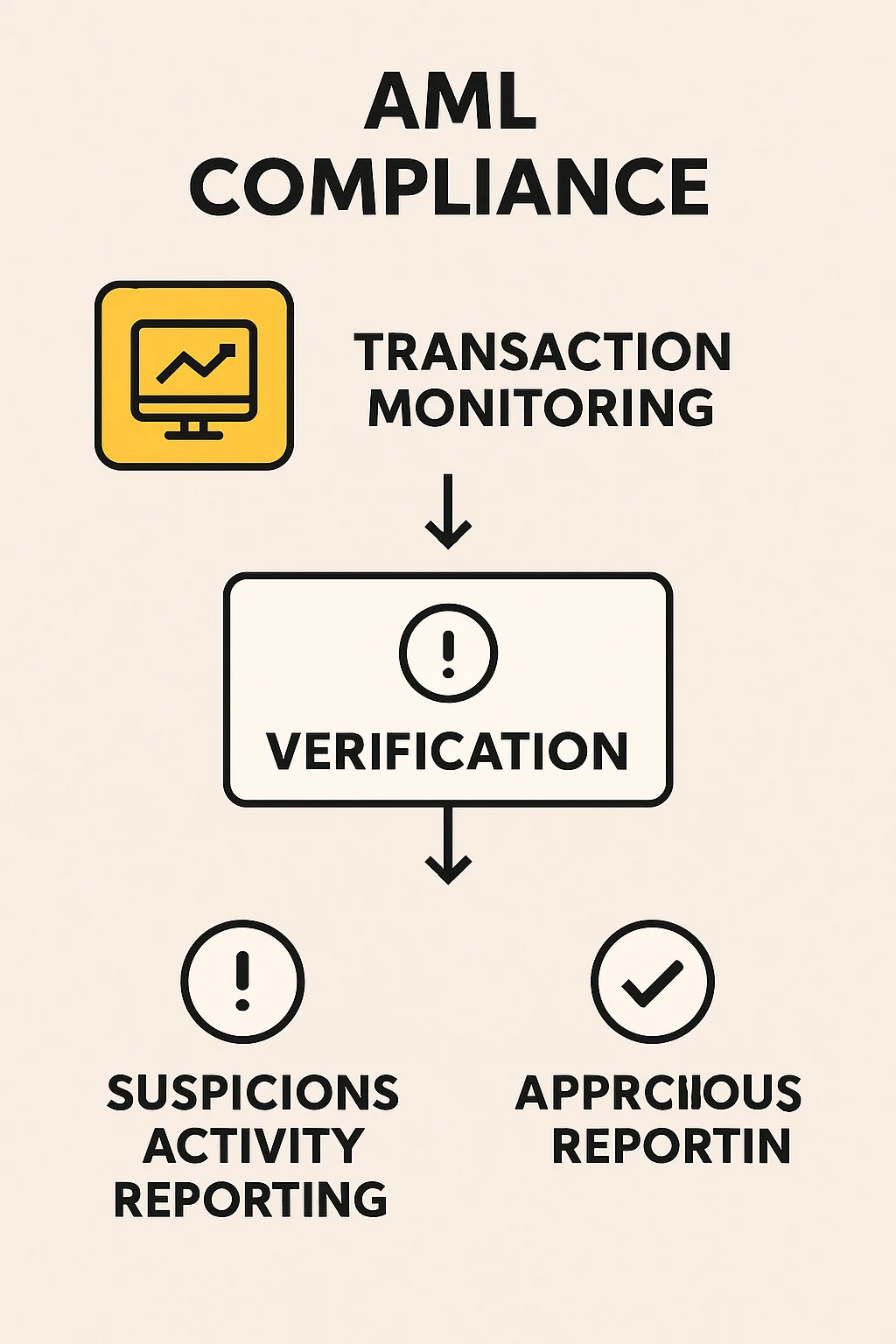
AML regulations force crypto businesses to monitor and report suspicious activities. It’s the government’s attempt to prevent crypto from becoming a money laundering paradise.
Anti-Money Laundering (AML) refers to laws, regulations, and procedures designed to prevent criminals from disguising illegally obtained funds as legitimate income. Crypto exchanges and businesses must implement AML compliance to operate legally.
How AML Works in Crypto
Transaction monitoring systems flag unusual patterns like rapid large deposits, immediate withdrawals, or transactions with known high-risk addresses.
Suspicious Activity Reports (SARs) must be filed with government agencies when exchanges detect potential money laundering. This creates permanent records tied to user identities.
Chain analysis tools track crypto movements across addresses, making it harder to obscure transaction histories compared to traditional cash-based money laundering.
Real-World Examples
- Binance paid $4.3 billion in fines for AML violations and inadequate compliance
- Tornado Cash sanctions highlighted tensions between privacy tools and AML enforcement
- Exchange delistings of privacy coins like Monero due to AML compliance challenges
Why Beginners Should Care
AML compliance affects your crypto experience through identity verification requirements, transaction limits, and account monitoring that can trigger investigations.
Privacy expectations should be adjusted – regulated exchanges share transaction data with governments upon request. True privacy requires decentralized tools with their own risks.
Choose exchanges with strong compliance records like Kraken that balance regulatory requirements with user protection and transparent policies.
Related Terms: KYC, Exchange, Privacy Coin, Regulation
