Cold Wallet
Cold Wallet Backup: Securing Your Security
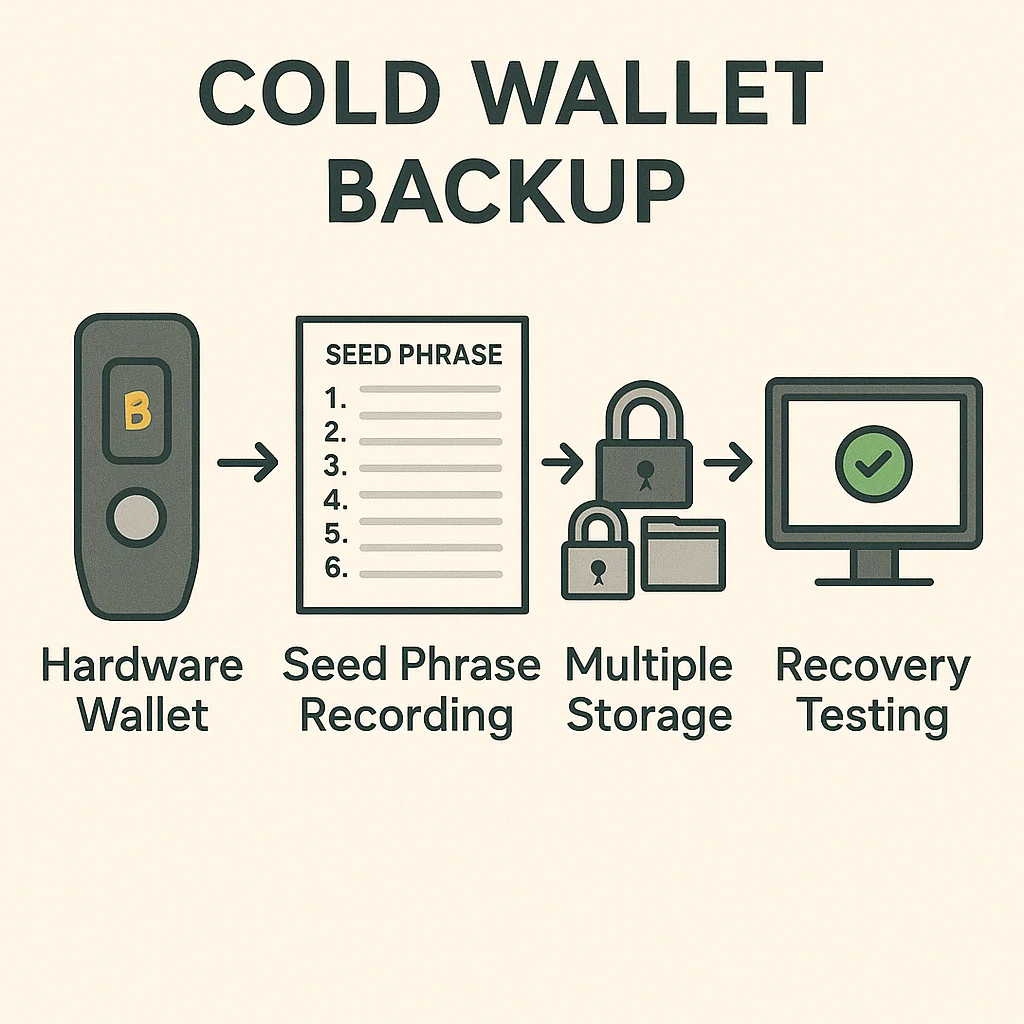
Cold wallet backup ensures you can recover your cryptocurrency even if your hardware wallet is lost, stolen, or destroyed. It’s like having spare keys to your safe deposit box.
Cold wallet backup refers to secure storage methods for seed phrases and recovery information that enable restoring access to hardware wallets and cold storage systems. Proper backup prevents permanent loss of funds due to device failure or loss.
How Cold Wallet Backup Works
Seed phrase storage involves securely recording the 12-24 word recovery phrase that can regenerate all wallet addresses and private keys.
Multiple backup methods include paper storage, metal engraving, and distributed storage across secure locations to prevent single points of failure.
Verification testing ensures backup information actually works by testing recovery procedures with small amounts before trusting large holdings.
Real-World Examples
- Metal seed storage using steel plates that resist fire, flood, and corrosion damage
- Bank safety deposit boxes for storing written seed phrases in secure, controlled environments
- Distributed storage splitting seed phrases across multiple secure locations
Why Beginners Should Care
Permanent loss prevention since cryptocurrency recovery is impossible without proper backup procedures, unlike traditional banking systems.
Inheritance planning enables family members to access cryptocurrency holdings in case of death or incapacitation through proper backup sharing.
Security balance between accessibility for legitimate recovery and protection from theft or unauthorized access to backup materials.
Related Terms: Hardware Wallet, Seed Phrase, Cold Storage, Recovery
