L2 Sequencer
L2 Sequencer: Transaction Ordering Engine
L2 sequencers determine transaction order on Layer 2 networks, controlling which transactions get included and how they’re arranged. They’re like traffic controllers for blockchain highways.
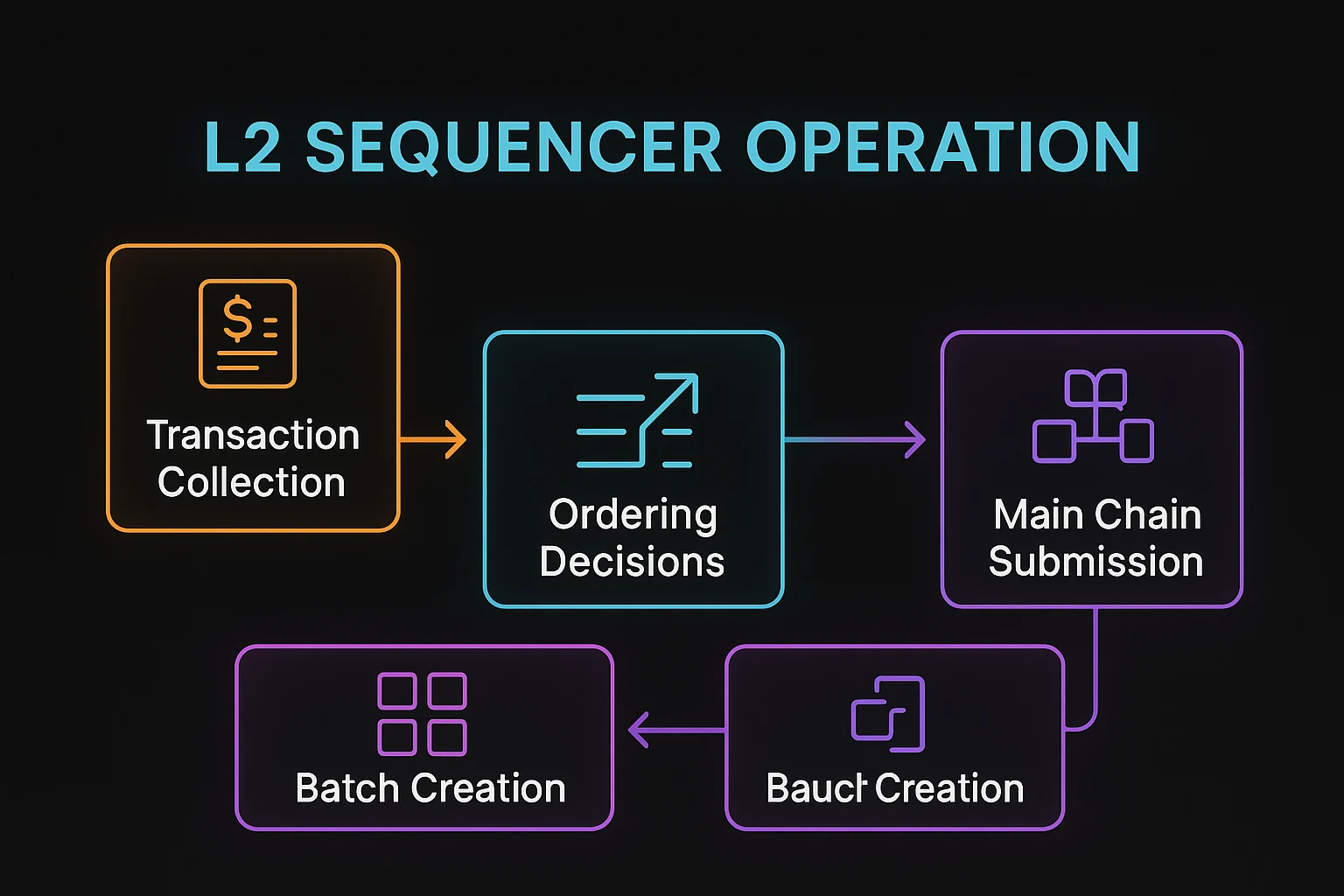
An L2 sequencer is a specialized node that collects, orders, and batches transactions for Layer 2 networks before submitting them to the main blockchain. Sequencers have significant power over transaction inclusion and ordering.
How L2 Sequencers Work
Transaction collection gathers user transactions from various sources and creates ordered sequences for batch processing.
MEV extraction opportunities arise from sequencers’ ability to reorder transactions, potentially front-running or sandwiching user trades.
Batch submission packages multiple transactions into single submissions to the main chain, amortizing costs across many users.
Real-World Examples
- Arbitrum sequencer operated by Offchain Labs with plans for decentralization
- Optimism runs centralized sequencing with revenue sharing for public goods funding
- Base uses Coinbase-operated sequencing with similar centralization trade-offs
Why Beginners Should Care
Centralization risks as most L2s currently use single sequencers that could censor transactions or extract MEV unfairly.
Performance benefits from centralized sequencing that enables faster transaction confirmation and better user experience.
Decentralization roadmaps vary among L2 providers, with different timelines and approaches for reducing sequencer centralization.
Related Terms: Layer 2, MEV, Transaction Ordering, Centralization Risk
