Optimistic Rollup
Optimistic Rollup: Trust but Verify Scaling
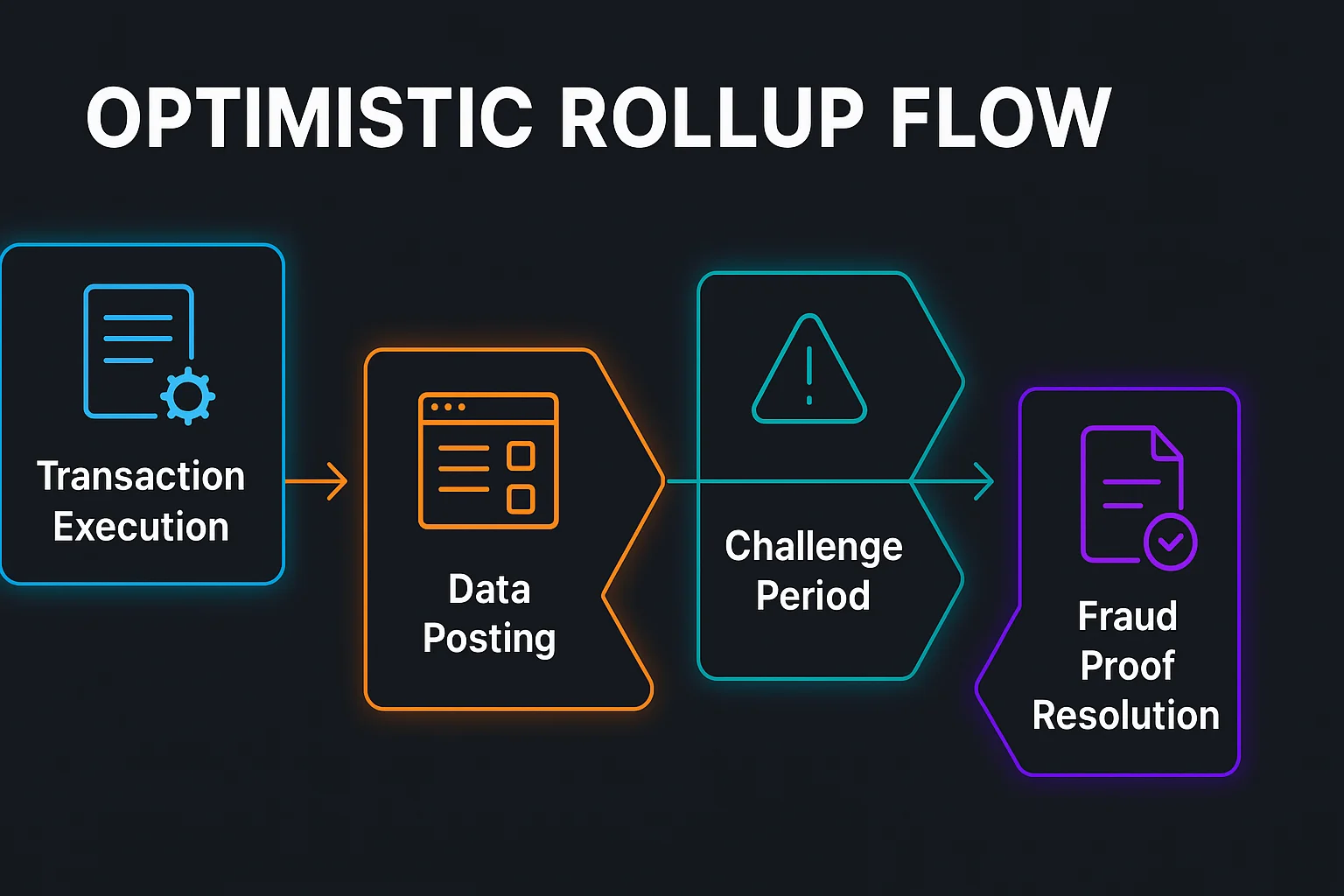
Optimistic rollups assume transactions are valid by default but allow challenges during dispute periods. It’s like innocent until proven guilty for blockchain transactions.
An optimistic rollup is a Layer 2 scaling solution that assumes transactions are valid by default and only verifies them if someone submits a fraud proof during a challenge period. This enables fast, cheap transactions while maintaining security through economic incentives.
How Optimistic Rollups Work
Optimistic execution processes transactions immediately without validation, posting transaction data to the main chain for availability.
Challenge periods allow anyone to submit fraud proofs if they detect invalid transactions, with economic penalties for false challenges.
Fraud proofs enable verification of specific transactions without re-executing entire blocks, making dispute resolution efficient.
Real-World Examples
- Arbitrum is the largest optimistic rollup with billions in TVL and major DeFi protocols
- Optimism focuses on public goods funding and retroactive rewards for ecosystem development
- Polygon Hermez (now zkEVM) started as an optimistic rollup before transitioning to ZK proofs
Why Beginners Should Care
Fast finality for most transactions since optimistic assumptions allow immediate execution without waiting for complex validation.
Withdrawal delays typically require 7-day challenge periods before funds can be moved back to Ethereum mainnet.
Lower costs compared to Ethereum mainnet while maintaining strong security guarantees through fraud proof mechanisms.
Related Terms: Layer 2, Fraud Proof, Challenge Period, Rollups
