Seed Phrase
Seed Phrase: Your Crypto Recovery Backup
Your seed phrase is your crypto’s ultimate backup. More important than passwords, more valuable than the device itself.
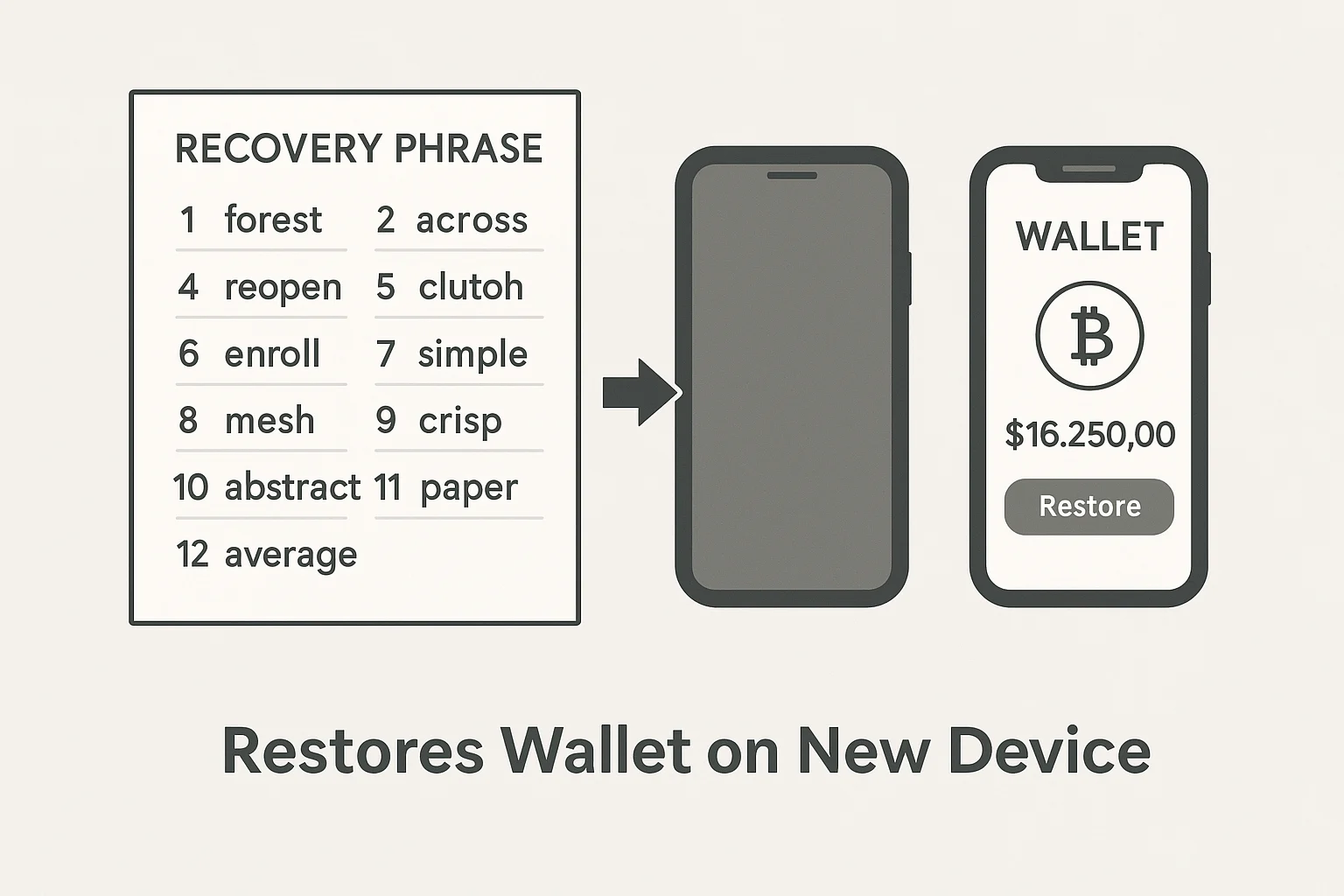
A seed phrase is a list of 12-24 words that can restore access to all your cryptocurrency wallets and funds. It’s your master key – lose it and your crypto is gone forever. Write it down and guard it with your life.
How Seed Phrases Work
When you create a crypto wallet, it generates a unique seed phrase from a list of 2,048 possible words. This phrase mathematically generates all your private keys and wallet addresses.
Think of it as a master password that recreates your entire wallet on any compatible device. Your actual wallet app is just an interface – the seed phrase IS your wallet.
These 12-24 words contain enough entropy to make guessing impossible. There are more possible combinations than atoms in the observable universe.
Real-World Examples
- Lost phone? Enter your seed phrase into a new wallet app and everything’s restored
- Hardware wallet breaks? Use your seed phrase with any compatible device
- Inheritance planning – Your seed phrase lets family access your crypto
Why Beginners Should Care
Seed phrases are your crypto insurance policy. Hardware can break, software can corrupt, but a properly stored seed phrase recovers everything.
Never store seed phrases digitally. Write them on paper or engrave them on metal. Never photograph them. Never store them in cloud services or password managers.
Many crypto users make small purchases to practice wallet recovery with their seed phrase before trusting it with larger amounts.
Related Terms: Private Key, Hardware Wallet, Wallet Recovery, Cold Storage
