Proof of Humanity
Proof of Humanity: Verifying Human Uniqueness
Proof of Humanity creates registries of verified unique humans to prevent Sybil attacks in voting and distribution systems. It’s like having a bouncer who knows everyone isn’t wearing a disguise.
Proof of Humanity is a system for creating verifiable registries of unique human beings to prevent individuals from claiming multiple identities in democratic or distribution systems. It aims to enable “one person, one vote” in digital contexts.
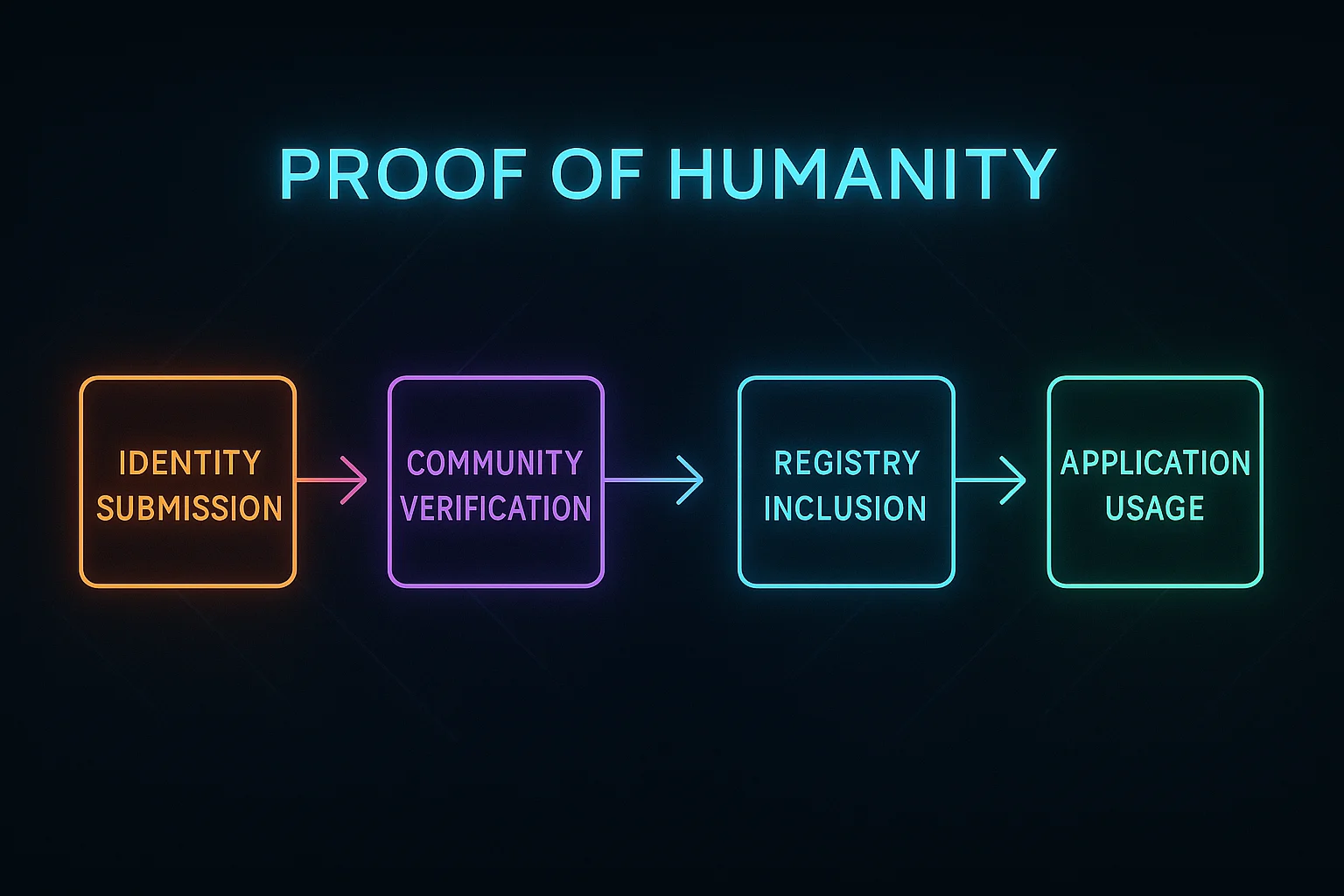
How Proof of Humanity Works
Identity verification through video submissions, vouching systems, and social verification to establish that each registration represents a unique human being.
Continuous validation requires periodic renewal and community challenges to maintain registry accuracy and remove fake or duplicate entries.
Application integration enables other protocols to use humanity verification for fair voting, airdrops, or governance participation.
Real-World Examples
- Proof of Humanity protocol creates Ethereum-based registries of verified humans
- Worldcoin uses biometric iris scanning for humanity verification
- BrightID relies on social graph analysis to identify unique humans
Why Beginners Should Care
Democratic participation in crypto governance systems that need to prevent wealthy individuals from claiming multiple votes through fake identities.
Fair distribution mechanisms for airdrops and universal basic income programs that should reach real people rather than bot farms.
Privacy trade-offs as humanity verification often requires revealing personal information or biometric data to prove uniqueness.
Related Terms: Sybil Attack, Anti-Sybil Mechanism, Democratic Governance
