Mining Pool
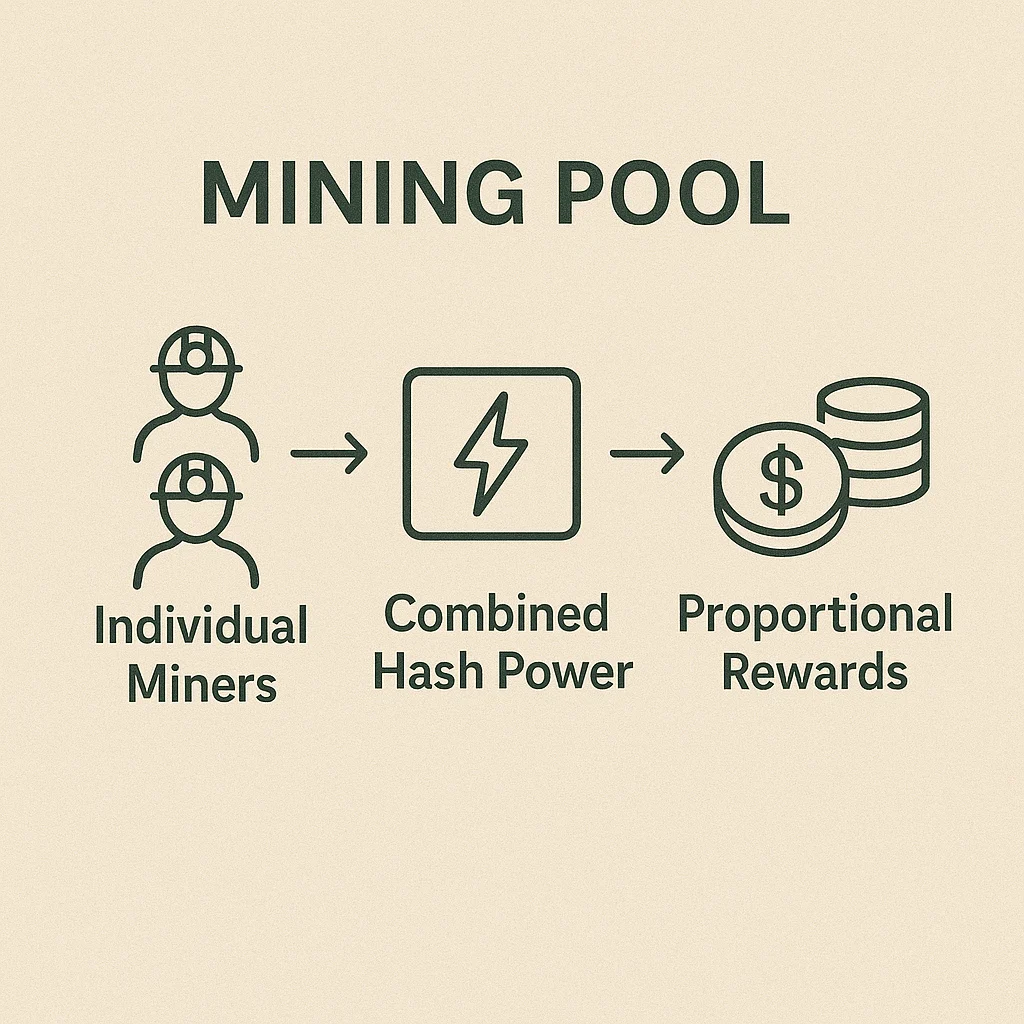
Mining Pool: Collaborative Block Mining
Mining pools combine computational power from multiple miners to increase chances of finding blocks and earning rewards. It’s like joining a lottery syndicate to improve your odds.
A mining pool is a collaborative group of cryptocurrency miners who combine their computational resources to increase their chances of successfully mining blocks and earning rewards. Pool participants share rewards proportionally based on their contributed computing power.
How Mining Pools Work
Resource pooling combines hash power from many individual miners to compete more effectively against large mining operations.
Reward distribution splits block rewards and transaction fees among pool participants based on their proportional contribution to the pool’s total hash rate.
Consistent payouts provide more regular income compared to solo mining, where individual miners might wait months between successful blocks.
Real-World Examples
- Antpool and F2Pool are among the largest Bitcoin mining pools by hash rate
- Ethereum mining pools like Ethermine dominated before the Proof of Stake transition
- Small miners typically join pools to receive steady income rather than gambling on solo mining
Why Beginners Should Care
Income stability through pooled mining provides predictable returns rather than the feast-or-famine nature of solo mining.
Lower barriers to mining participation since small miners can earn proportional rewards without needing massive infrastructure investments.
Centralization concerns as large pools could theoretically coordinate to attack networks, though economic incentives discourage this behavior.
Related Terms: Mining, Hash Rate, Block Reward, Proof of Work
