Multi-Chain
Multi-Chain: Using Multiple Blockchain Networks
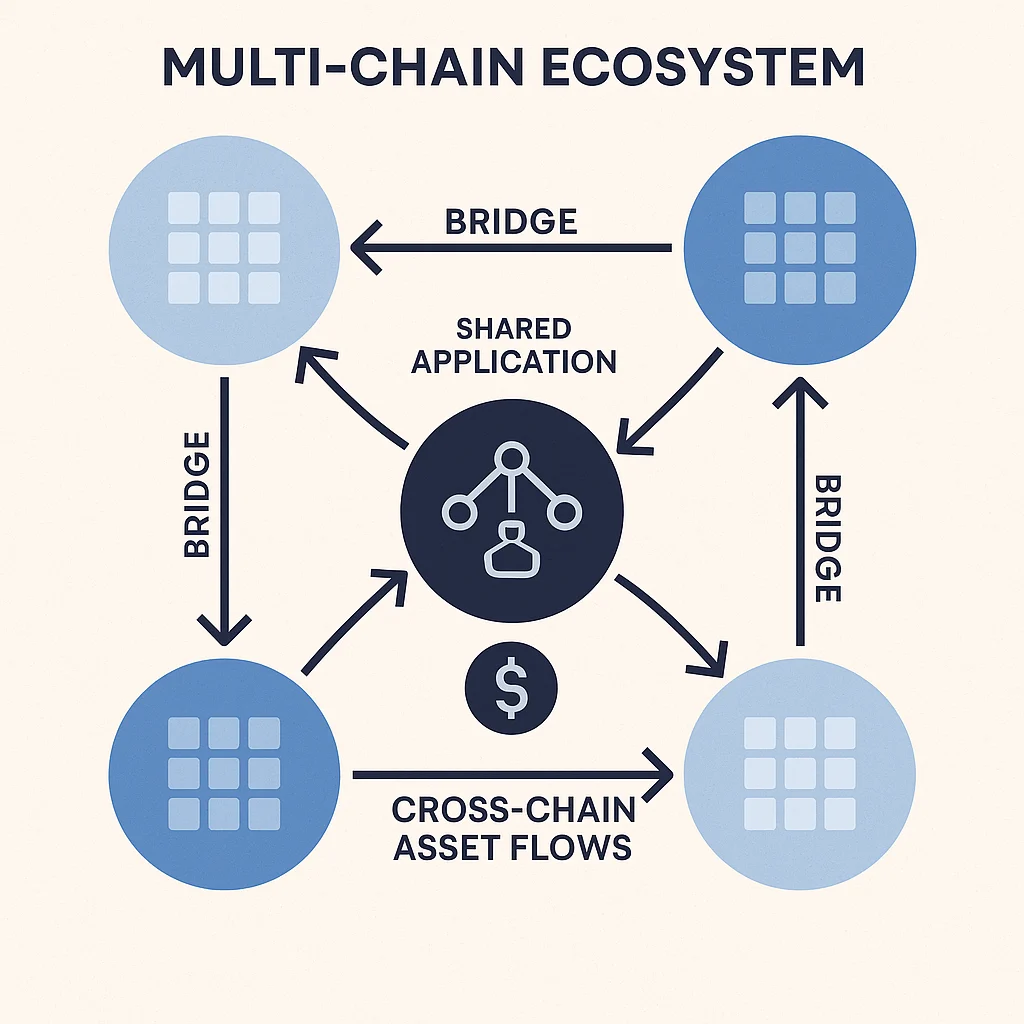
Multi-chain refers to applications, strategies, or ecosystems that operate across multiple different blockchain networks simultaneously. It’s like being multilingual in the blockchain world.
Multi-chain describes systems that utilize multiple different blockchain networks rather than being limited to a single chain. This approach leverages the unique strengths of different blockchains while diversifying risks and expanding capabilities.
How Multi-Chain Works
Cross-chain integration enables applications to operate on multiple blockchains, accessing different user bases, liquidity sources, and technological capabilities.
Bridge infrastructure connects different blockchain networks, allowing assets and data to move between chains through various technical mechanisms.
Strategic diversification spreads risks and opportunities across multiple networks rather than depending entirely on one blockchain’s success or failure.
Real-World Examples
- Aave operates lending markets on Ethereum, Polygon, Avalanche, and other networks
- Uniswap has deployed on multiple chains to access different user communities
- USDC stablecoin exists natively on over 15 different blockchain networks
Why Beginners Should Care
Diversified exposure reduces risks from any single blockchain network experiencing technical problems, regulatory issues, or adoption challenges.
Expanded opportunities as different chains offer unique applications, lower fees, or better performance for specific use cases.
Complexity management since multi-chain strategies require understanding multiple networks, bridge risks, and cross-chain coordination challenges.
Related Terms: Cross-Chain, Bridge, Interoperability, Chain Abstraction
