Rug Pull
Rug Pull: When Projects Disappear With Your Money
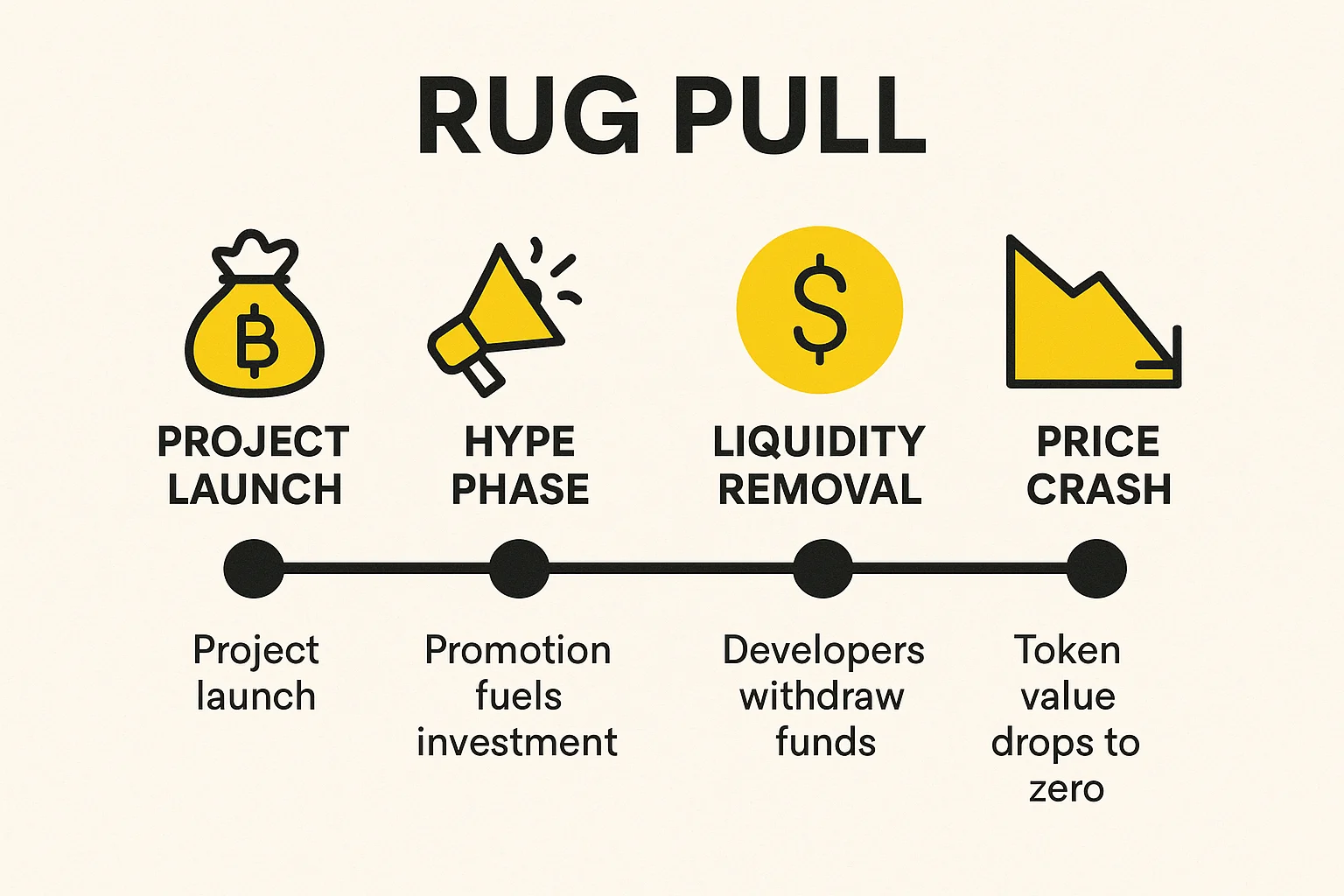
Rug pulls are crypto’s version of old-fashioned exit scams. Developers build hype, collect investor money, then vanish into the digital night.
A rug pull is when cryptocurrency project developers abandon the project and steal investor funds. The term comes from “pulling the rug out” from under investors who trusted the project.
How Rug Pulls Work
Soft rug pulls involve developers gradually selling their tokens while hyping the project, slowly draining liquidity without obvious theft. The project eventually dies from lack of development.
Hard rug pulls are more dramatic – developers remove all liquidity from trading pools, making tokens worthless overnight. Investors wake up to find their tokens can’t be sold.
Smart contract backdoors allow developers to mint unlimited tokens or drain funds directly from the contract, even after launch. The code looks legitimate but contains hidden functions.
Real-World Examples
- Squid Game Token – Gained 2,300% then crashed 99% when developers pulled liquidity
- AnubisDAO – Raised $60 million then disappeared within 20 hours
- Meerkat Finance – $31 million “hack” that looked suspiciously like an inside job
Why Beginners Should Care
New DeFi projects launch daily, many created specifically to rug pull investors. If returns seem too good to be true, they probably are.
Research thoroughly before investing in new projects. Check if tokens are locked, if the team is doxxed (publicly known), and if the smart contract has been audited by reputable firms.
Never invest more than you can afford to lose in experimental DeFi projects, especially those promising unrealistic returns.
Related Terms: Smart Contract, Liquidity Pool, Token Lock, Phishing Attack
