Smart Contract
Smart Contract: Code That Enforces Agreements
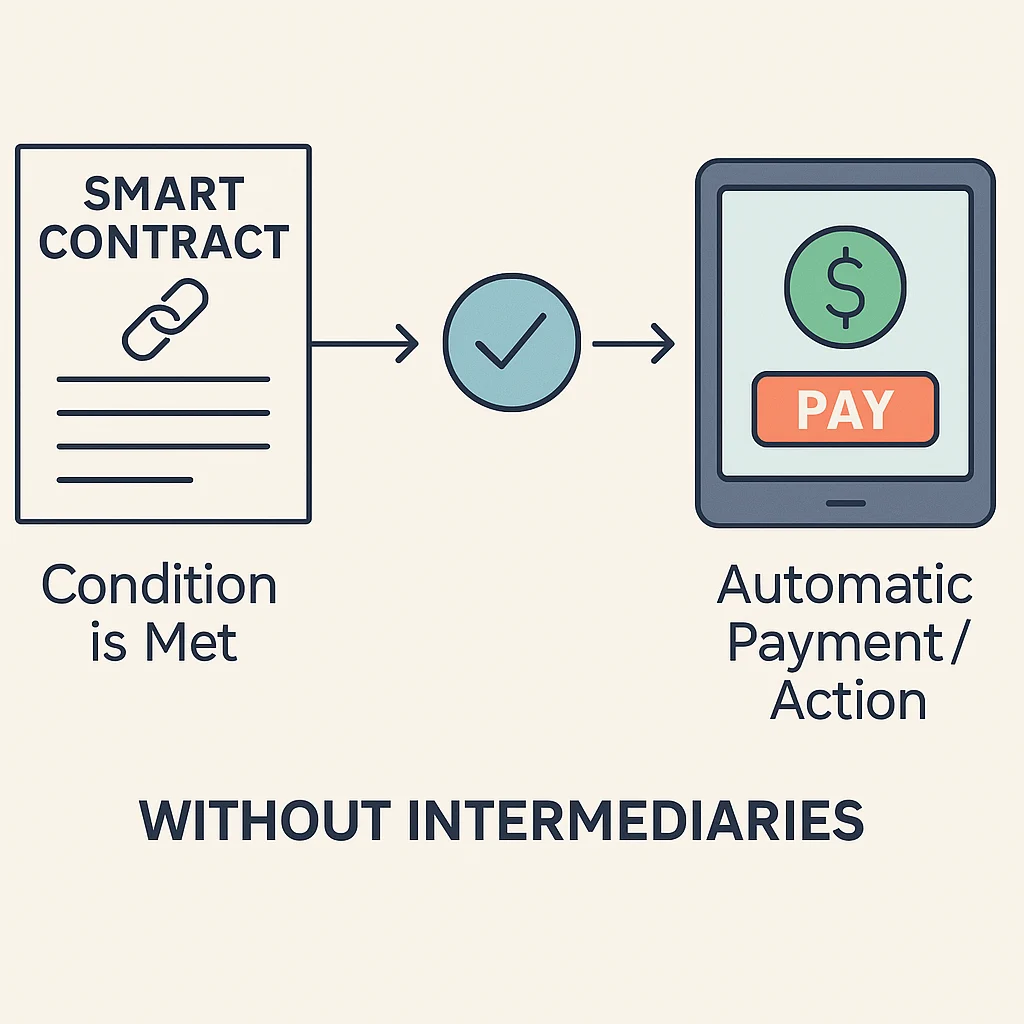
Smart contracts are why crypto is bigger than just digital money. They’re agreements that execute themselves automatically when conditions are met.
A smart contract is computer code that automatically executes agreement terms when predetermined conditions are satisfied. No lawyers, no courts, no arguing – just math and code enforcing the deal.
How Smart Contracts Work
Think of a vending machine. You insert money, select a product, and the machine automatically gives you your snack. Smart contracts work similarly – they hold funds and release them when specific conditions are met.
These contracts run on blockchain networks like Ethereum. Once deployed, they can’t be changed or stopped, ensuring all parties get exactly what was programmed.
The code is public and auditable. Everyone can verify exactly how the contract works before interacting with it.
Real-World Examples
- DeFi lending – Deposit collateral, automatically receive a loan
- Insurance payouts – Flight delayed? Smart contract pays you automatically
- NFT marketplaces – Buy NFT, payment and ownership transfer happen instantly
Why Beginners Should Care
Smart contracts eliminate middlemen who take fees and add delays. They create trustless systems where you don’t need to trust the other party – you trust the code.
This powers decentralized finance (DeFi), where you can lend, borrow, and trade without traditional banks. No credit checks, no paperwork, just code executing agreements fairly.
