Proof of Work (PoW)
Proof of Work (PoW): Bitcoin’s Security Model
Proof of Work is how Bitcoin solves the double-spending problem without trusted authorities. It’s energy-intensive by design – that’s a feature, not a bug.
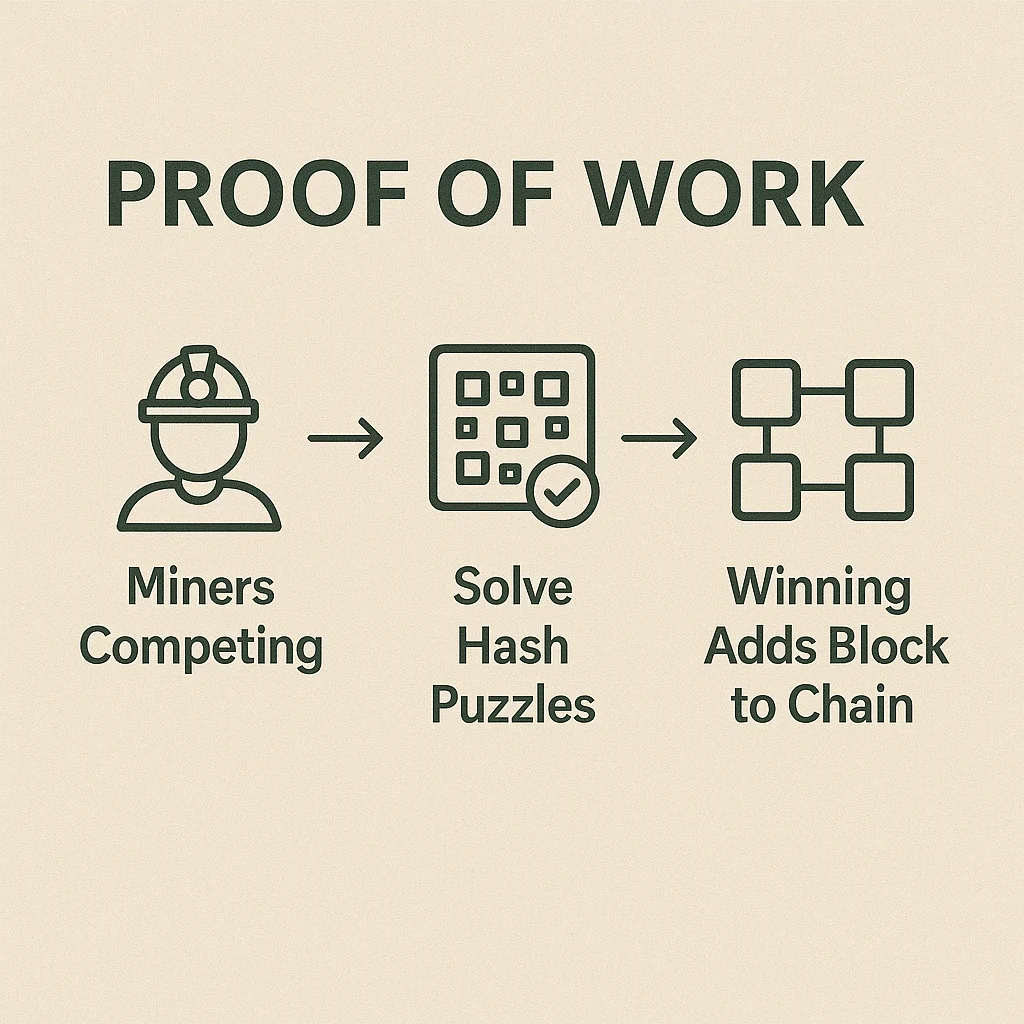
Proof of Work is a consensus mechanism where miners compete to solve computationally difficult puzzles to validate transactions and create new blocks. The winning miner earns newly created cryptocurrency plus transaction fees.
How Proof of Work Functions
Miners race to find a nonce (random number) that, when hashed with block data, produces a result starting with a specific number of zeros. This requires enormous computational power but is easy to verify.
Network difficulty adjusts automatically to maintain consistent block times regardless of total mining power. More miners join, difficulty increases. Miners leave, difficulty decreases.
Economic security comes from the cost of attacking the network. To control Bitcoin, you’d need 51% of global hash rate – requiring billions in mining equipment and ongoing electricity costs.
Real-World Examples
- Bitcoin uses SHA-256 hashing algorithm with ~10-minute block times
- Litecoin uses Scrypt algorithm designed to be ASIC-resistant (though ASICs eventually emerged)
- Monero regularly changes algorithms to maintain CPU/GPU mining accessibility
Why Beginners Should Care
Proof of Work provides proven security through economic incentives rather than trust in authorities. Bitcoin’s PoW has operated continuously for 15+ years without successful attacks.
Energy consumption is controversial but provides real security. The electricity cost makes attacks expensive while securing hundreds of billions in value.
Alternative consensus mechanisms like Proof of Stake are newer and less battle-tested, though they consume much less energy.
Related Terms: Mining, Hash Rate, Proof of Stake, 51% Attack
