Session Keys
Session Keys: Temporary Wallet Permissions
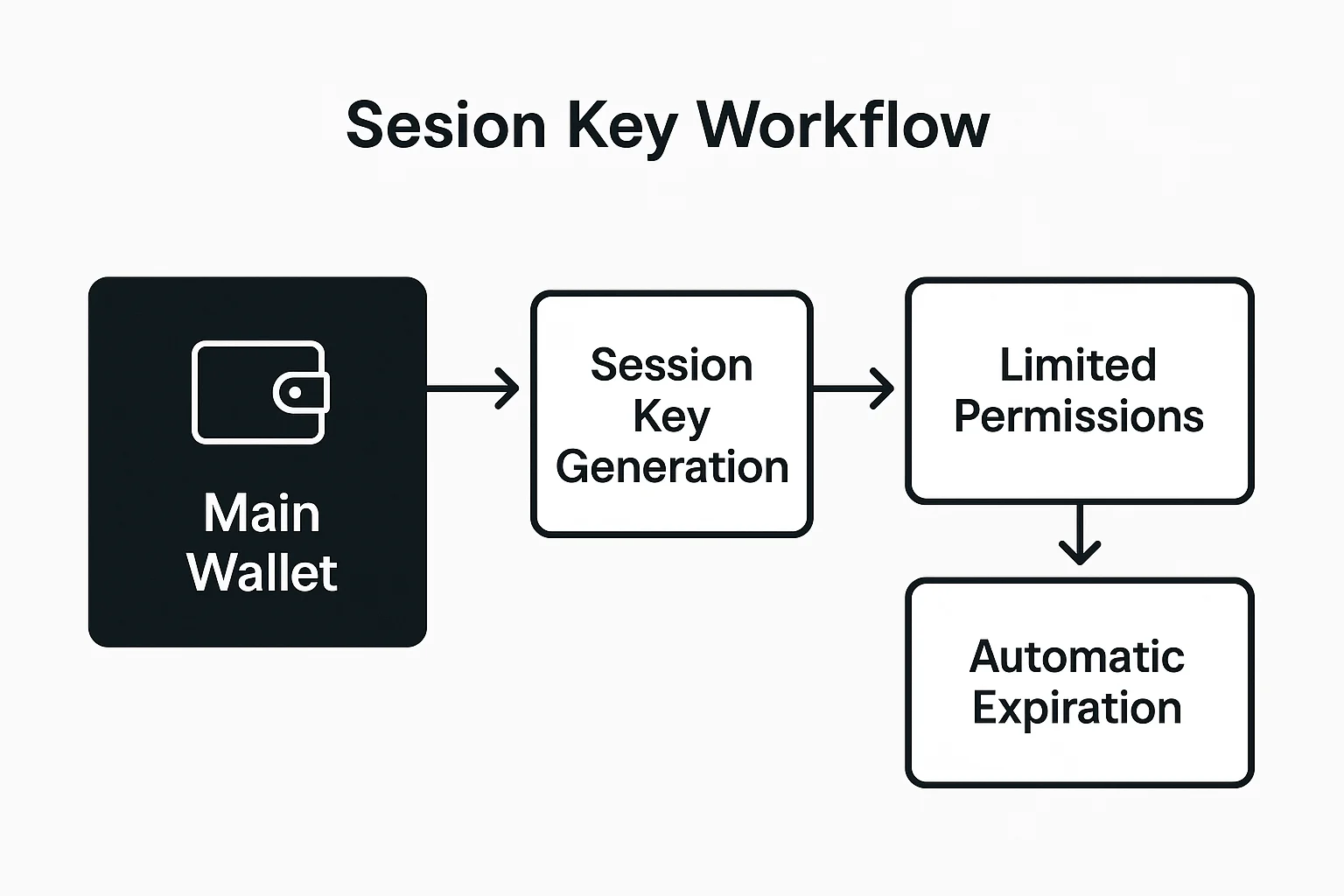
Session keys provide temporary, limited permissions for applications to perform specific actions without exposing main wallet private keys. It’s like giving valet keys instead of your full car keys.
Session keys are temporary cryptographic keys that grant limited permissions to applications for specific time periods or transaction types. They enable seamless user experiences while maintaining security through restricted access scope.
How Session Keys Work
Permission scoping limits what actions session keys can perform, such as trading specific tokens, interacting with certain contracts, or spending up to defined amounts.
Time expiration automatically revokes session key access after predetermined periods, preventing indefinite exposure if keys are compromised.
Revocation mechanisms allow users to immediately cancel session keys if they detect suspicious activity or no longer want to grant access.
Real-World Examples
- Gaming applications use session keys for in-game transactions without requiring wallet approval for every action
- DeFi protocols enable automated trading strategies with spending limits and time constraints
- Mobile wallets create session keys for app interactions while keeping main keys in secure storage
Why Beginners Should Care
Improved UX eliminates constant wallet approval prompts for routine actions while maintaining security through limited permission scope.
Risk reduction means compromised session keys can only perform limited actions rather than providing full wallet access to attackers.
Automation enablement allows complex multi-step operations to execute automatically within predefined parameters without manual intervention.
Related Terms: Account Abstraction, Smart Contract, Security
