MEV (Maximal Extractable Value)
MEV (Maximal Extractable Value): The Hidden Tax on DeFi
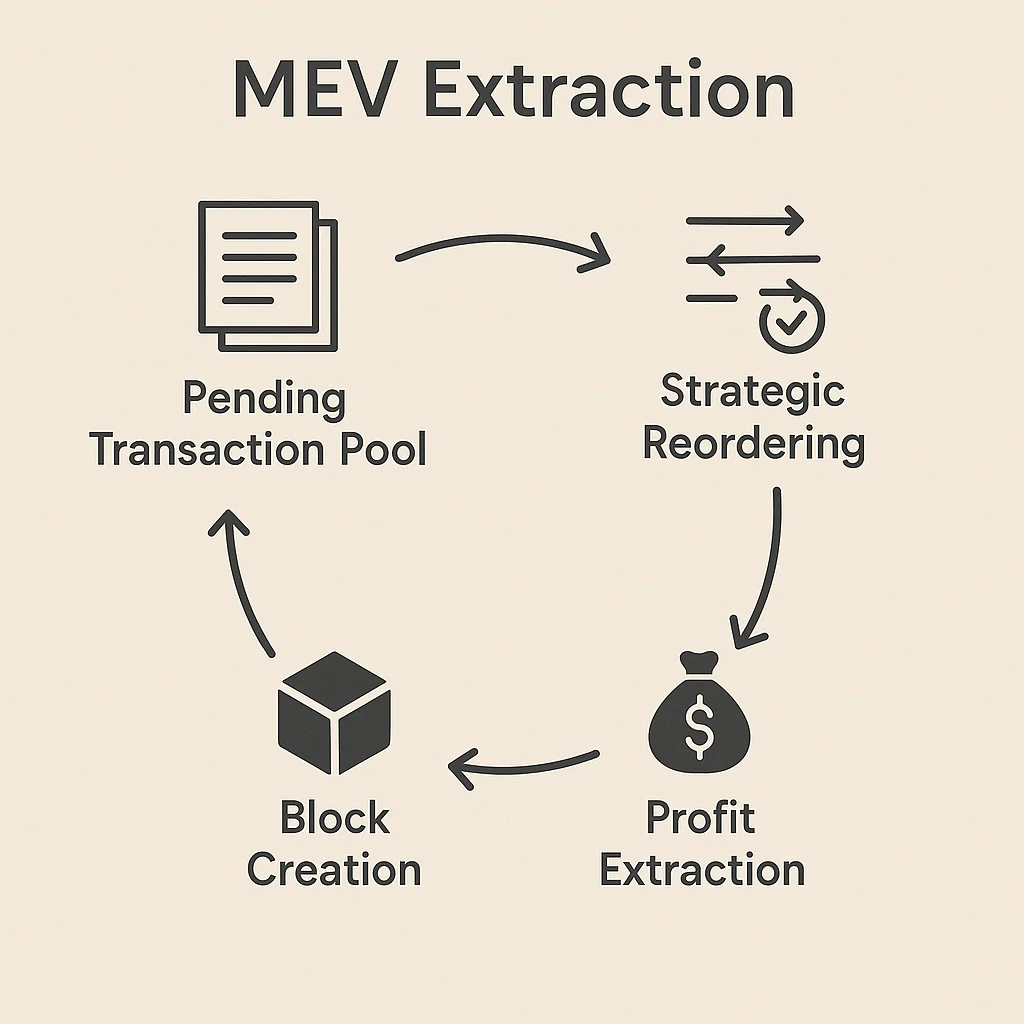
MEV is the extra profit that miners and validators can extract by reordering, including, or excluding transactions within blocks. It’s like cutting in line at the blockchain cafeteria.
Maximal Extractable Value (MEV) is the additional profit that block producers can capture by strategically ordering transactions, beyond standard block rewards and fees. This creates an invisible tax on DeFi users through front-running, sandwich attacks, and arbitrage extraction.
How MEV Works
Transaction ordering power lets miners and validators see pending transactions and arrange them to maximize their profit, often at the expense of regular users.
Front-running involves placing transactions ahead of known profitable trades to capture arbitrage opportunities or cause slippage for the original trader.
Sandwich attacks place transactions before and after target trades to manipulate prices and extract value from the victim’s transaction through artificial slippage.
Real-World Examples
- DEX arbitrage bots extract millions daily by front-running price differences between exchanges
- Liquidation sniping involves front-running liquidation transactions to capture discounted collateral
- NFT sniping uses MEV to front-run popular NFT purchases and flip for immediate profit
Why Beginners Should Care
Hidden costs from MEV can significantly increase the real cost of DeFi transactions beyond visible gas fees through increased slippage and worse execution prices.
Protection strategies include using private mempools, MEV-protected RPC endpoints, or protocols specifically designed to prevent MEV extraction.
Ecosystem impact sees billions in value extracted from regular users annually, raising questions about fairness and sustainability of current blockchain designs.
Related Terms: Front-Running, Sandwich Attack, Slippage, DeFi
