Zero-Knowledge Proof (ZKP)
Zero-Knowledge Proof (ZKP): Proving Without Revealing
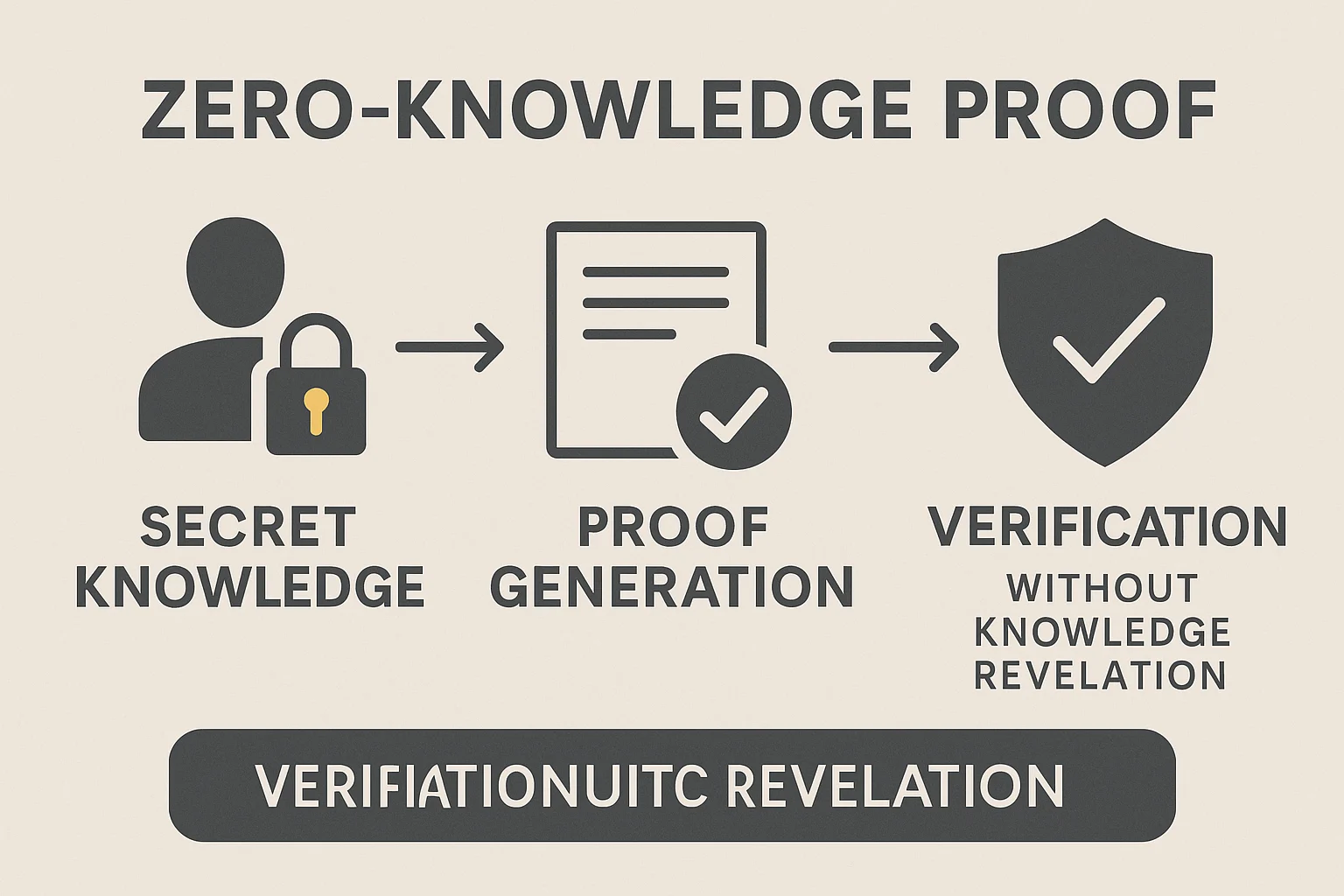
Zero-knowledge proofs let you prove you know something without revealing what you know. It’s like proving you’re over 21 without showing your birth date, address, or any other personal information.
A zero-knowledge proof (ZKP) is a cryptographic method that allows one party to prove they possess certain information without revealing the information itself. The verifier learns nothing except that the prover’s claim is true.
How Zero-Knowledge Proofs Work
Mathematical magic creates proofs that are computationally infeasible to fake but easy to verify. The prover demonstrates knowledge through complex calculations that would be impossible without the secret information.
Three properties define valid zero-knowledge proofs: completeness (honest provers can convince verifiers), soundness (dishonest provers cannot convince verifiers), and zero-knowledge (verifiers learn nothing beyond claim validity).
Practical applications include proving account balances without revealing amounts, demonstrating identity without sharing personal data, or validating transaction history without exposing details.
Real-World Examples
- Zcash transactions use zk-SNARKs to prove transaction validity without revealing amounts or addresses
- Polygon Hermez uses zero-knowledge rollups for scalable Ethereum transactions
- Age verification systems prove you’re over 18 without revealing your exact age or birthday
Why Beginners Should Care
Privacy revolution potential exists as ZKPs enable verification systems that don’t require sharing sensitive personal or financial information.
Scalability solutions like zk-rollups use zero-knowledge proofs to batch thousands of transactions while maintaining security and reducing costs.
Technical complexity makes ZKPs challenging to implement correctly, but user-facing applications hide this complexity behind simple interfaces.
Related Terms: Privacy Coin, zk-SNARKs, zk-STARKs, Rollups
