ZK Proof Aggregation
ZK Proof Aggregation: Scaling Zero-Knowledge Systems
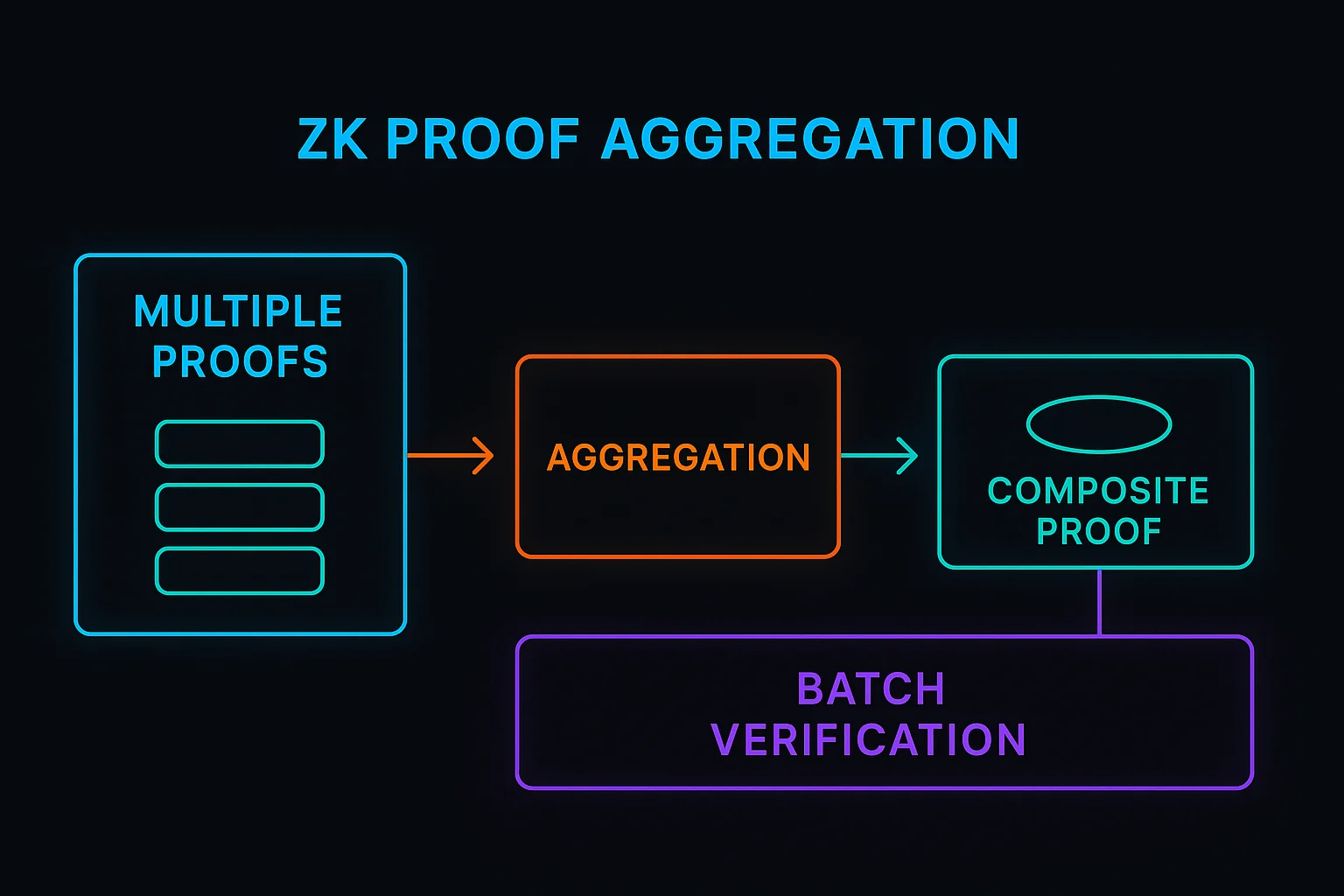
ZK proof aggregation combines multiple zero-knowledge proofs into single, more efficient proofs. It’s like having one master key that proves you have access to multiple locked boxes.
ZK proof aggregation is a technique that combines multiple zero-knowledge proofs into a single proof that verifies all the original statements simultaneously. This dramatically reduces verification costs and blockchain storage requirements.
How ZK Proof Aggregation Works
Batch verification processes multiple proofs together rather than verifying each one individually, reducing computational overhead significantly.
Recursive composition enables proofs about proofs, where one ZK proof can verify that other ZK proofs are valid without revealing their contents.
Cost amortization spreads verification costs across many transactions, making ZK systems economically viable for smaller value transactions.
Real-World Examples
- StarkNet uses STARK proof aggregation for scalable transaction processing
- Polygon Hermez combines multiple transaction proofs into batches for Ethereum submission
- Mina Protocol uses recursive zk-SNARKs to maintain constant blockchain size
Why Beginners Should Care
Scalability improvements enable ZK systems to handle transaction volumes comparable to traditional centralized systems.
Cost reduction makes ZK privacy and verification accessible for everyday transactions rather than only high-value use cases.
Technical complexity requires sophisticated cryptographic infrastructure that few teams can implement correctly.
Related Terms: Zero-Knowledge Proof, Recursive Proofs, Batch Verification, Scalability
